If you run a website, manage a business inbox, or even just use online banking, you’ve already lived in the phishing era for a long time. The only thing that’s changed is the polish.
Phishing scams have moved past those obviously fake “please verify” requests to include convincing login pages, realistic invoices, and even bogus delivery updates. Some are mass-sent and easy to spot, others are customized precisely for the person they’re targeting, their job, company, tech, and everyday apps.
Today phishing is one of the most common front doors attackers use to get what they want: access. Access to accounts, access to money, access to admin panels, access to customer data, access to infrastructure. And once an attacker has access, they can pivot quickly into malware infections, account takeovers, or ransomware.
Below we’ll break down what phishing is, how it works, the common types you’re most likely to see, and what you can do as a website owner to reduce your risk.
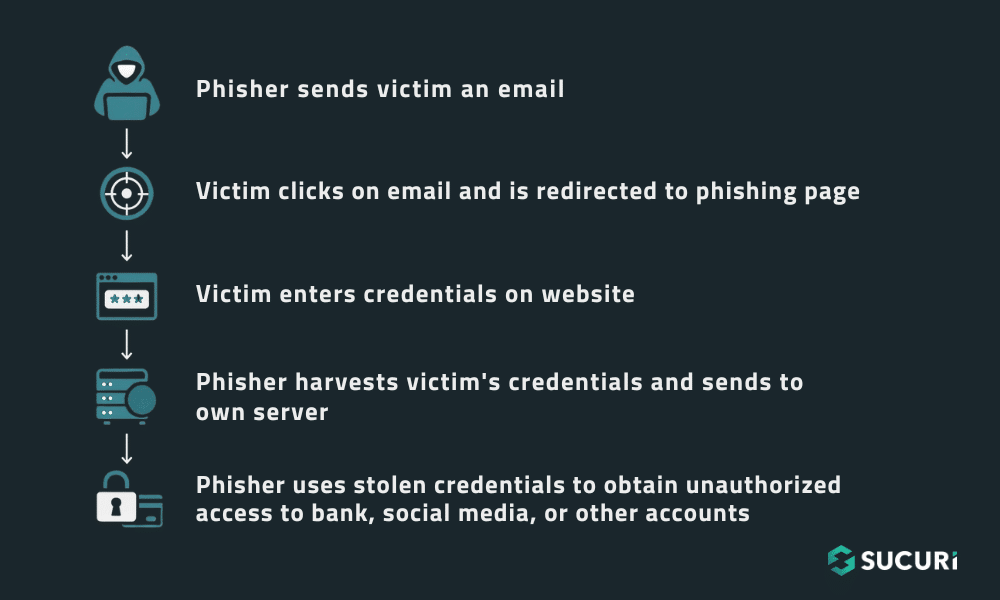
What actually happens in a phishing attack?
Most phishing attacks are simple at the surface, yet their outcomes are often destructive. This is the typical sequence of events that turns a harmless-looking message into a real security incident.
1) The attacker picks a believable “story”
A phishing email or text message always has a narrative that makes sense in the context of daily digital life, creating the initial hook. The goal isn’t to be creative, it’s to be entirely plausible. Common stories revolve around scenarios that demand attention, such as a notice claiming, “We detected suspicious activity,” or “Your account will be suspended.” Other compelling narratives include transactional issues like, “Your payment failed,” or a fake invoice you supposedly requested. Attackers also use common events like “Your package is waiting” or a request to “Can you review this document?”
2) The message creates pressure
Phishers rely heavily on urgency because it is the most effective way to reduce careful, critical thinking. You’ll see this manipulation in language that stresses immediate compliance, using phrases like “Action required,” “Final notice,” “Last chance,” or demanding “Immediate verification” within 24 hours. This pressure can be fear-based, such as an alert about “fraud detected,” or sometimes reward-based (“you’ve been selected”). In spear phishing, it can be relationship-based, with a supposed colleague asking, “Hey, can you do this quickly?”
3) You’re directed to do one risky thing
Once the trust is established and the pressure is on, the message directs the target toward a single, risky action. That “one thing” is the point of no return, which turns a simple message into a security incident. The common calls-to-action are clicking a malicious link, opening a file attachment, calling a fraudulent phone number, replying with sensitive information, or, most commonly, entering credentials on a fake login page.
4) The attacker collects something valuable
The outcomes of phishing generally fall into two major buckets, and often, it’s both.
Bucket A is data theft, where the primary goal is to steal critical information. This includes usernames and passwords, credit card or bank information, personal data used for identity theft, internal company information, or crucial multi-factor authentication codes.
Bucket B is malware delivery. In this scenario, the user’s action leads to the deployment of malicious software, such as malware that steals saved passwords or browser sessions, ransomware that locks files until a ransom is paid, or remote access tools that grant attackers persistent control over the system. It’s common for an attacker to steal access first and then use that compromised foothold to push malware later.
The common types of phishing you’ll see
Phishing has expanded far beyond the email inbox. Attackers follow attention, which means their tactics now target every major communication platform.
Email Phishing (the classic)
Email phishing is the broad, high-volume style most people visualize. An attacker blasts a large list of addresses and hopes a small percentage of recipients click. This method is common because it’s cheap, highly scalable and yes, remains effective. It frequently involves brand impersonation (faking banks, hosting providers, or payment systems), prompts to reset passwords, alerts about an “unusual login,” fake invoices, or fake customer complaints with malicious links.
Spear Phishing
Spear phishing is what happens when attackers stop guessing and start researching. Instead of sending 10,000 generic emails, they send 10 carefully crafted, highly personalized ones. These messages might include your name, your specific job role, the tools your team uses, details about a real vendor your company works with, or personal details scraped from public sources like LinkedIn. Its danger lies in its authenticity; it feels legitimate because it was specifically designed for you.
Whaling
This is simply spear phishing aimed at the highest levels of power: executives, finance leads, and company owners. Attackers target these individuals because a single compromised executive account can unlock wire transfers, payroll changes, sensitive documents, and privileged administrative access. Whaling attempts are often extremely convincing and timed around busy periods like quarter-end, tax season, or major company launches.
URL Phishing
URL phishing relies on domains that are “close enough” to fool a person at a quick glance. Attackers use common tricks like intentional misspellings (“micros0ft” style swaps), adding extra words to a legitimate domain (“secure-login-…”), or confusing subdomains (placing a legitimate-looking word before an unrelated domain). The attacker then hosts a page that perfectly mirrors a real login or payment screen. The trap is that the page looks perfect, but the actual URL tells the truth about the fraudulent destination.
Smishing
This method uses SMS text messages. This is effective because texts feel immediate and informal, meaning people don’t typically examine them with the same caution they apply to emails. Popular smishing themes include delivery notices, urgent bank alerts, warnings saying “your account is locked,” and fake support messages, all designed to elicit an instant tap on a malicious link.
Vishing (phone phishing)
These attacks occur through phone calls or voicemail. The attacker impersonates a trusted entity (a bank, tech support, a government agency, or a vendor), anyone who can justify asking for sensitive personal data. They are typically looking for account details, verification information, access codes, payment information, or trying to convince you to install “support software,” which is often just malware.
Pharming
A more technical cousin of phishing. Instead of tricking you into clicking a fake link, the attacker redirects you behind the scenes, sometimes by compromising DNS settings or local network configurations. This is particularly scary because it can bypass the confidence gained by checking or even typing the correct URL. It reinforces why layered protection is essential, as security is never reliant on a single habit.
The tactics phishers use and why they work
Phishing campaigns are not random; they are built on psychological patterns. Understanding these patterns is key to spotting them quickly.
1) Social engineering: the psychological shortcut
Phishers attempt to put the recipient into a mental state of compliance where they act without critical thought. They achieve this using a spectrum of emotional triggers: manufactured urgency, invoking authority (e.g., “I’m the CEO, do this now”), fear (“fraud detected”), curiosity (“see the document”), scarcity (“final notice”), or manipulative helpfulness (“support team here to fix your issue”).
2) Fake login pages (the “mirror site”)
This is a primary tactic for credential theft. Attackers frequently clone real login pages for popular services like email providers, WordPress admin screens, hosting dashboards, and payment portals. If you enter credentials into the fake form, the attacker receives them instantly. To cover their tracks, you are often redirected to the real site after submitting, leading you to assume you simply mistyped your password the first time.
3) Email spoofing
Spoofing makes an email appear to originate from a trusted source. This can be as simple as forging the “From” field or using a lookalike domain that is close enough to pass a quick review. It’s a vital reminder that a familiar display name is not proof; always check the actual sender address and its domain.
4) Pop-ups and fake alerts
While browsing, you may encounter pop-ups that signal either a compromised website or adware on your device. Any pop-up asking you to log in again or download security software should be treated as highly suspicious until you can verify its legitimacy. Reputable services almost never collect sensitive information through random, unexpected pop-ups.
5) Malware attachments and drive-by downloads
The phishing message often contains a malicious file disguised as an “invoice,” “statement,” or “document.” Alternatively, the link itself may trigger a “drive-by download” of malware or ransomware. This demonstrates why the defense isn’t just about protecting your password given a single opened attachment could be enough to compromise your entire system.
Why phishing is especially risky for website owners
If you own or manage a website, the stakes are significantly higher. You are not just protecting your personal accounts; you are a custodian of your customers, your revenue, your brand reputation, your email deliverability, and your search visibility. Phishing often acts as the entry point for a catastrophic website security incident.
Admin access is a high-value prize
If an attacker successfully obtains your WordPress admin login, hosting credentials, cPanel access, or FTP/SFTP access, they can pivot quickly. With this level of access, they can create new malicious admin users, inject scripts into your site, redirect visitors to scams, steal any stored customer data, install backdoors for persistent access, lock you out of your own site, and even use your server to distribute malware to other targets. One stolen password can lead to a complete site compromise.
Your site can be repurposed as a phishing platform
This is a nightmare scenario. Your trusted website is compromised and then used by attackers to host phishing pages or redirect unsuspecting traffic. Visitors who trust your domain may fall for the attack precisely because it’s hosted on your URL. This rapid compromise can lead to immediate browser warnings, blacklisting by search engines, massive loss of customer trust, and reputational damage that lasts long after the cleanup is complete.
Business email compromise can spill into customer fraud
When your business email is compromised, attackers can seamlessly impersonate your staff and communicate directly with your customers. They can start altering invoice details, fraudulently requesting payments, asking customers for “verification” (stealing their data), and harvesting sensitive customer information. This is one of the quickest ways a phishing attack can evolve into a financial and reputational crisis for your entire business.
“I clicked the link.” What to do next
If you clicked a phishing link or, worse, entered information, do not freeze. A fast and decisive response can prevent a bad day from becoming a full-blown disaster.
Step 1: Report it immediately
Mark the message as phishing in your email client, as this helps train filters and block future campaigns. If you are part of an organization, notify your IT or security contact immediately.
Step 2: Change passwords (starting with email)
This is the most crucial step. If your email is compromised, attackers can use it to reset passwords for every other service. Prioritize the password change for your email, followed by your hosting/CMS access, financial accounts, and then every other account where that password was reused.
Step 3: Enable MFA/2FA everywhere possible
Multi-Factor Authentication makes stolen passwords significantly less useful. If you can only enable it on a few accounts, focus on your email, hosting provider, WordPress admin, payment processor, and banking services.
Step 4: Check for suspicious activity
You need to look for signs of unauthorized access, such as login alerts, new devices registered to your account, password reset emails you didn’t request, unexpected forwarding rules in your email settings, new admin users in your CMS, and unexpected file changes on your website.
Step 5: Run security scans and update systems
If you downloaded anything, you must assume malware is possible. Run full endpoint protection scans on your device, patch your operating system and browser, and update all website plugins, themes, and core files. If you manage a site, scan it thoroughly for malware.
Step 6: Contact banks/providers if financial info was involved
If any payment details or personal financial information were submitted, call your bank or card issuer right away. The sooner you report, the more options you typically have for mitigating financial damage.
Step 7: Report Significant Incidents to Authorities
If the attack involves significant fraud or identity theft, you may need to involve local authorities. Their involvement is often necessary, especially for reporting and documentation.
Phishing prevention that actually fits real life
No one can “be perfectly cautious” 24/7. The goal of real-world security is to build a few high-impact habits and add security layers that protect you for the moments when your attention inevitably slips.
Build better click habits
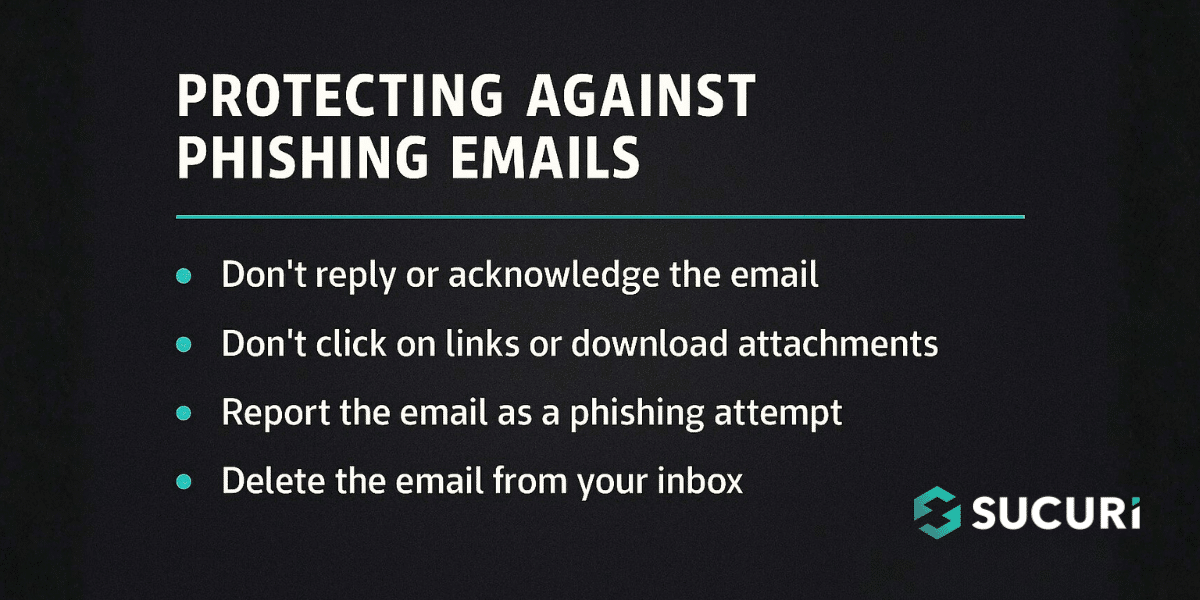
Before clicking any link, consider:
- Was I expecting this message?
- Is the sender’s actual address exactly correct?
- Is the URL legitimate when I hover over it?
- Am I being rushed?
- Is this asking for credentials, payment, or MFA codes?
- Can I verify this through an unrelated, separate channel?
When in doubt, bypass the link entirely and navigate to the official site directly by typing the address, using a saved bookmark, or accessing your official dashboard.
You need to keep software updated
Updates are rarely just for features; they are critical security patches that close known holes attackers exploit. Regularly update your browser, operating system, antivirus/endpoint protection, password manager, WordPress core, themes, plugins, and server software. Outdated software makes the attacker’s job significantly easier once they get a foothold via phishing.
Use strong authentication
This is foundational. Use unique, complex passwords for your most important accounts (e.g., email, hosting, CMS), and use a password manager to make this realistic and sustainable. And turn on MFA/2FA wherever it is offered. Phishers thrive on password reuse because it turns one compromised account into ten.
Protect your website like it’s a business asset
Finally, if you manage a site, you can’t rely on good luck. You need layered defenses: implement a Website Application Firewall (WAF) to block known malicious traffic, apply hardened admin access (MFA, strong unique passwords, limited login attempts), maintain regular backups for quick recovery, set up continuous monitoring for early compromise detection, and run routine malware scanning. This layered approach, which guides the Sucuri mindset, means you assume threats will happen and design your security to keep the blast radius small.
A quick takeaway
Phishing is one of the most common entry points leading to severe security incidents across the board, including account takeovers, website compromises, malware and ransomware events, customer data exposure, and lasting brand reputation damage.
The most effective defense is a blend of strategies, not one magic tool or perfect behavior:
- Awareness: Learn to spot the common patterns and triggers.
- Verification: Slow down and verify before you click.
- Authentication: Use unique passwords and strong MFA.
- Patching: Close known security holes by keeping all software current.
- Website Security Layers: Implement a firewall, monitoring, and reliable backups for your site.
Phishing attacks are persistent, but they are absolutely not unbeatable. By adopting a few better security habits and installing the right layered protections, you can make you and your website a far more difficult target.











